Series 5: PII security methods
How to store PII information securely
Personally identifiable information (PII) refers to data that can be used to contact, locate and identify an individual, and ideally feature information like phone number, name, medical records, date of birth, age, credit card information, and so on. Just about all organizations use and store PII for information regarding their customers, clients or employees. Several schools, universities, and hospitals store PII of their students and patients as well.
As companies collect, process, and store PII, they must also accept the responsibility of ensuring the protection of such sensitive data. A single careless worker can lead to PII being shared with unauthorized individuals, and falling into the wrong hands. No matter how the data is lost, its responsibility will invariably fall on the shoulder of the company.

The PII stored by a company faces security threats from online attackers who desire to sell the data in the black market in exchange for a good sum of money. This data can be used for a variety of criminal activities, such as social engineering attacks, identity theft, and fraud.
Hence, it is prudent that companies and individuals try their best to protect their PII and have certain systematic security measures in place for it. Failure to protect their PII would leave a firm open to heavy regulatory fines and targeted social engineering attacks, as well as a result in loss of customer loyalty.
Here are a few measures a company can take to securely store or present PII while querying:
1. Data Masking

Data masking is a process used to protect PII or other types of sensitive information – such as passwords – from unauthorized access via obfuscation by replacing key values with charachters such as ‘*’. thus protecting sensitive data – such as employee salaries or customers’ credit card numbers – from displaying in applications.
Data Masking can be a standard feature in the components used in architecture – such as Dynamic Data Masking in Azure Synapse or Azure SQL Database.
In components where Dynamic Data Masking is not supported out of the box – a copy of the same data physically masked can be prepared in a separate table or file – and access governed by using RBAC supported by the component. This approach can be used for instance in Azure Data Bricks.
2. Encryption
This is among the most prominent pressures used by organizations for Data Loss Prevention (DLP). With encryption, a company can protect their company from cybercriminals who are looking for ways to access sensitive data and also prevent employees from making any mistake that results in loss of data.
Lifecycle of a Company’s Data
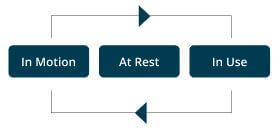
It is a pendant to encrypt data across all three stages, as PII can be intercepted by threat actors at any of them. It additionally is vital to take note that no matter how good encryption is, its effectiveness will largely depend on the people using it.
Hence, the employees of a firm should be trained frequently on both evolving threats and technology updates.

The following approaches are in general used for secure data access:.
1. Two-Factor and Multi-Factor Authentication

These security processes add an extra layer of security to the standard system of online identification with the usage of passwords. In most cases, people have to use a username and password to access sensitive information.
But with two-factor authentication, they shall be prompted to enter another authentication process, which can include fingerprint, password or Personal Identification Code.
When it comes to multi-factor authentication, people shall have to through more than two authentication processes subsequent to entering their password and username.
These processes can significantly assist in preventing cyber criminals from accessing PII as they are unlikely to have access to multiple devices used by a person to authenticate their identity.
2. Dispose or Destroy Old Media with Old Data
Data destruction and disposal are two vital aspects of protecting sensitive data. The security policies of a company should underline how long data can be kept, and the ways employees can destroy or dispose it.
They can ideally use the following steps for this purpose

Clearing
Overwriting the media
Purging
Magnetic erasure of the media

Destruction
Physical destruction of the media
3. Use a firewall and antivirus
Both software and hardware-based firewalls can be used as a barrier between a device and the internet connection, and prevent hackers from accessing sensitive data and files.
Antivirus software would ideally compile a database of malicious malware and viruses trying to obtain access to a device and data, and make sure that they are unable to do so.
In addition to following the security practices mentioned above, a company should also have an acceptable usage policy (AUP) in place for accessing PII. Such a policy shall clearly define who can access PII and the ways they can use it.
AUP will serve as a jumping-off point for developing technology-based controls with the aim of reinforcing systematic PII storage and usage tactics.


